Nigerian registrants. Dodgy Eastern European host offering bulletproof and anonymous hosting. Yup, I very much doubt there is anything legitimate at all hosted on 188.241.58.60.. or indeed any part of Qhoster's network.
237buzz.com
255page.ga
702mine.com
779999977.com
a1cargomovers.com
abtprinting.com
adassco.com
admincamac.co.uk
afazendaideal.ml
afflluenceindia.com
africheck.com
alamiranut.com
alexandrahospitals.com
alliarnce.org.uk
allseaship.com
amba-medias.com
amiicogroup.com
andrzejkupnopark.eu
anook.info
ansaexpress.com
antrackdiplomaticcs.com
apidexconstruction.com
aramexbe.com
arshland.com
artyschat.com
atlanticfforum.com
aughana.com
battlegrounds-arena.com
baugeruest-handel.com
bevadgmbh.com
billdiamondfinance.co.uk
binaryoptionsmonitor.com
binco-sale.com
bit-masters.com
bitcoincashold.com
bitcoinsdrugsrehab.com
bitmain-alliances.com
bitmamashop.com
blecoman.com
bmpro.info
bourseafrique.com
britannia-pharmaceutical.co.uk
btccap.biz
btctriplermachine.com
buycounterfeitmoneys.com
calvinscott.biz
cameroonianbeauties.com
candodvillahotel.com
carphonewarehouse-eu.com
centroculturadigital.com
certificatesshop.com
chainconnect.co
chaseoffshoreonline.tk
chondomonitor.com
citydiaryfarms.com
classicdeliverycourier.com
clickhereforgiveaway.site
clickhereforgiveaway.xyz
cloud-bigfile.com
cncoslight-zh.com
cnximgang.com
coca-colafinancedept.com
coflaxfluidhandling.com
coinminners.com
coinrxstore.com
compasseguip.com
confirmedsoft.us
cosm0-hk.com
cosmosport24.com
creditonfcu.com
crewlinked.com
criagent.com
crypto023.com
cryptominingtechnology.com
cryptoshifters.com
cs-oilfeild.com
cureonlinepharmacy.org
denverlaserhairremoval.co
divecastle.com
dlnamicatrade.com
double-bitcoins-legit.com
eastmanimpex.cam
ebid-tg.com
efceosaudi.com
elitecertifiedhack.com
emailtime.info
ethiopianairilines.com
eurocertificationcentre.eu
fabftifun.com
faircloths.co.uk
fastcoine.com
fastestfingersfirst.com
fidelity-investment.co.uk
findingthepropercode.com
firstsuorceinc.com
forvisitingthankyou.com
fotesale.com
front-dashboard.com
gdp-international.com
general-funds.com
generate-dcash.biz
gettinginonthelow.com
global-news.center
globalinkscobsult.com
globalinksconsult.com
gmb-trade.com
goimsa.info
grand-sale.com
grantersmultiservices.com
greetapex.com
guaranteecds.com
hackers-list.com.de
harpack-ulma.com
heraeu.com
hereweareonit.com
hlroyoung.com
horizonpartnerrsltd.com
houseofspells.com
hsbrands-int.ml
humer1adminka.com
hyip.co.in
hyipcave.com
idexpresscargo.com
inlinefornine.com
interseadrill.com
item-desc.com
jdfrencis.com
jonihoppershowcase.com
kcf-th.com
kececiprofile.com
kencanafishing.com
kiingsay.com
kindres.com
kindres.de
kippaskagit.com
kmsinfoservice.com
ks-prod.com
lane-pres.com
legitrxonline.club
lifegoalsdevelopmentschool.com
litbitcoinembassy.com
littlerockbitcoins.com
live-rx-store.com
loactrippleser.ga
loan-assistance.com
loan-dealer.com
loudiclear.com
lurnentum.com
luwiex.com
manarpso.com
mannhiem.in
maomanlodocs.cf
marshawoifesquire.com
mcmg-tech.com
meetcameroonians.com
meetup4real.com
megachemstoreonline.com
miamibeachcoin.com
microclicker.com
mile22-casting.com
miningcrux.com
mission4christministry.com
movimientorevolucionariodelpueblo.org
ms-fi.com
mst4sale.com
mysite111.com
neatwaytogettheninth.com
neusportltd.com
news-world.center
nexttys.com
nightcapdice.com
ninthinline.com
nlsteinweg.com
nomuta.com
noworri.com
obsgruop.com
offshoreseadrill.com
onehereisreservedforyou.com
online-citibankgroup.com
ontothenextgame.com
opcolage.com
orifiameglobal.com
ourskynet.com
oxfords-pay.com
parcelservicess.com
pharmas4plus.com
plccsolutions.com
psypharm.com
ptochart.com
quicktitletransfer.com
rashedal-wataniagroup.com
rawgarner.com
realbuyrx.com
recordspharm.com
researchchem4us.com
resumedatabase11.xyz
rnailb.com
rnarhaba.com
ro-noutati-mondene.ml
robnsaconsult.com
rock-sale.com
rosenbaumcontemporarygroup.com
royalstandard.ga
rumlt.in
rush-sale.com
seachiefs.com
seguradoravirtual.com
seosenior.com
service-infoo.com
she-afro.com
shippingdynamics.com
showbarghana.com
siglobal.org
simplyitaly.dk
simplyitaly.it
skillocademy.com
sms-red-online.ga
solid-sale.com
southchina-sea.net
srcoin.ca
srnec-cn.com
stacksign.ga
superenterprise.work
superwhiteningpills.org
svclnlk.com
tax-gov.com
tccholdng-th.com
tecebusiness.com
techfronst.com
thebinaryoptionmonitor.org
thecolumbiabanks.com
thefutureofkitchen.com
theninthisin.com
thewomoorsfestival.co.uk
thisistheninth.com
tienhongjs.com
timetorefillthestock.com
torromodel.de
trans-atlanticdrilling.com
trustedhackers.com
turkiyenews247.tk
turkiyenews27.tk
twhe48.online
uk-pharmcay.com
ulmaparkaging.com
ultronnews.com
unipharma.bz
urnalaxmi-organics.com
usr-acc-serv.com
vendadebitcoin.com
visteonogbonnagroup.com
vpox.ru
vwork.pw
walletsofcoolandhip.com
weather-livenews.com
webs-host.pro
xcesstel.com
xopen.cc
yahoomailservice.com
youngcompamies.com
yoyooo.xyz
zestcrypto.com
Tuesday, 22 May 2018
Phishing and fraudulent sites hosted on 188.241.58.60 (Qhoster)
Thursday, 10 May 2018
Malware spam: "New documents available for download" / service@barclaysdownloads.co.uk / barclaysdownloads.com
This fake Barclays spam seems to lead to the Trickbot banking trojan.
The download password and submission number are the same in all cases I have seen. Clicking the link leads to a landing page at barclaysdownloads.com.
Entering the password downloads a document AccountDocuments.doc with a VirusTotal detection rate of 14/58, and Hybrid Analysis indicates that this uses an Equation Editor flaw to run a Powershell that downloads an additional component from:
http://basedow-bilder.de/kporto.bin
http://crimefiles.net/logo.bin
The .bin file is saved as %TEMP%\lovemete.exe and this currently has a detection rate of 15/65. Hybrid Analysis indicates this is Trickbot.
barclaysdownloads.co.uk and barclaysdownloads.com have both been registered for this purpose, the latter of which is hosted at Cloudflare.
From: Barclays [service@barclaysdownloads.co.uk]
Date: 10 May 2018, 13:16
Subject: New documents available for download
Signed by: barclaysdownloads.co.uk
Security: Standard encryption (TLS) Learn more
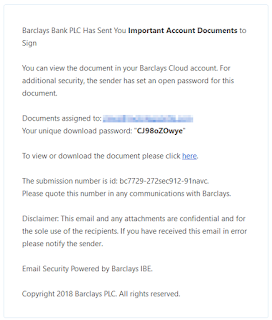
Barclays Bank PLC Has Sent You Important Account Documents to Sign
You can view the document in your Barclays Cloud account. For additional security, the sender has set an open password for this document.
Documents assigned to: jlines@[redacted]
Your unique download password: "CJ98oZOwye"
To view or download the document please click here.
The submission number is id: bc7729-272sec912-91navc.
Please quote this number in any communications with Barclays.
Disclaimer: This email and any attachments are confidential and for the sole use of the recipients. If you have received this email in error please notify the sender.
Email Security Powered by Barclays IBE.
Copyright 2018 Barclays PLC. All rights reserved.
The download password and submission number are the same in all cases I have seen. Clicking the link leads to a landing page at barclaysdownloads.com.
Entering the password downloads a document AccountDocuments.doc with a VirusTotal detection rate of 14/58, and Hybrid Analysis indicates that this uses an Equation Editor flaw to run a Powershell that downloads an additional component from:
http://basedow-bilder.de/kporto.bin
http://crimefiles.net/logo.bin
The .bin file is saved as %TEMP%\lovemete.exe and this currently has a detection rate of 15/65. Hybrid Analysis indicates this is Trickbot.
barclaysdownloads.co.uk and barclaysdownloads.com have both been registered for this purpose, the latter of which is hosted at Cloudflare.
Labels:
Cloudflare,
Malware,
Spam,
Viruses
Friday, 4 May 2018
"Best porno ever" Necurs spam
This spam (apparently from the Necurs botnet) promises much, but seems not to deliver.
I only saw four different links in the body text:
Warning live links - do not click
http://46.161.40.145:3314/
http://37.1.211.221:1699/
http://31.207.47.125/3FgtbvCf
http://77.72.84.115/
None of these sites were working when I tested them. Hosting IPs are:
46.161.40.145 (Ankas Ltd, Moldova)
37.1.211.221 (3NT Solutions, UK)
31.207.47.125 (Hostkey, Netherlands)
77.72.84.115 (Netup, UK)
3NT Solutions are a well-known purveyor of badness and I recommend blocking everthing, What the payload is here is unclear, but you can guarantee that's it's nothing good. And probably not smut either.
From: Susanne@victimdomain.tld [Susanne@victimdomain.tld]The sender's name varies, but is always in the same domain as the victim.
Date: 4 May 2018, 10:22
Subject: Best porno ever
Hi [redacted],
Best gay,teen,animal porno ever
Please click the following link to activate your account.
hxxp:||46.161.40.145:3314
Regards,
Susanne
I only saw four different links in the body text:
Warning live links - do not click
http://46.161.40.145:3314/
http://37.1.211.221:1699/
http://31.207.47.125/3FgtbvCf
http://77.72.84.115/
None of these sites were working when I tested them. Hosting IPs are:
46.161.40.145 (Ankas Ltd, Moldova)
37.1.211.221 (3NT Solutions, UK)
31.207.47.125 (Hostkey, Netherlands)
77.72.84.115 (Netup, UK)
3NT Solutions are a well-known purveyor of badness and I recommend blocking everthing, What the payload is here is unclear, but you can guarantee that's it's nothing good. And probably not smut either.
Labels:
inferno.name,
Malware,
Spam
Subscribe to:
Posts (Atom)